We Take CDP Security Seriously
You don’t compromise on your customers’ data security, and neither do we. Our processes, behaviors, and every level of our infrastructure are built with enterprise security in mind. Parce que nous servons les plus grandes entreprises du monde, mondialement distribuées et technologiquement matures, nous avons construit une customer data platform (CDP) qui résiste à l’examen le plus rigoureux des RSSI.Compliance
SOC 2 Type 2
Treasure Data fait l’objet d’un audit annuel SOC 2 de type 2 portant sur les critères des services de confiance (TSC) en matière de sécurité, de confidentialité, de disponibilité et d’intégrité du traitement (PI).
Obtenir une copieSOC 3
Treasure Data fait l’objet d’un audit annuel SOC 3 de type 2 portant sur les critères des services de confiance (TSC) en matière de sécurité, de confidentialité, de disponibilité et d’intégrité du traitement (PI).
Obtenir une copieISO/IEC 27001
Treasure Data fait l’objet d’un audit annuel de certification ISO27001:2022 portant sur le SMSI qui régit la CDP Treasure Data.
Obtenir une copieISO 27701
Treasure Data subit un audit annuel de certification ISO/IEC 27701:2019 sur le PIMS qui régit la CDP Treasure Data.
Obtenir une copieISO/IEC 27017
Treasure Data se soumet à un audit annuel de certification ISO/IEC 27017:2015 sur le SMSI qui régit la CDP Treasure Data.
Obtenir une copieISO/IEC 27018
Treasure Data se soumet à un audit annuel de certification ISO/IEC 27018:2019 sur le SMSI qui régit la CDP Treasure Data.
Obtenir une copieHIPAA Type 2
La conformité HIPAA garantit que Treasure Data protège la confidentialité, l’intégrité et la sécurité des ePHI pour nos clients des secteurs de la santé et des sciences de la vie. Treasure Data fait l’objet d’un audit annuel HIPAA de type 2 afin de vérifier que toutes les exigences de la règle de sécurité HIPAA sont prises en compte et fonctionnent efficacement.
Get audit reportCSA STAR Level 1
CSA Star niveau 1 est une auto-attestation destinée aux fournisseurs de services en nuage (CSP) qui valide l’utilisation par Treasure Datades meilleures pratiques de l’industrie pour sécuriser les données dans notre CDP.
Obtenir une copiePrivacy Mark
Treasure Data fait l’objet d’audits annuels de conformité au label PrivacyMark. PrivacyMark is a privacy-centric certification in Japan that focuses on enhancing consumers’ awareness of personally identifiable information (PII) protections. The requirements are based on JISQ standards and are governed by JIPDEC (Japan Institute for Promotion of Digital Economy and Community). PrivacyMark is viewed as the Japan equivalent of the ISO/IEC 27001.
Obtenir une copieFISC
Treasure Data a élaboré un guide pour aider nos clients à comprendre comment notre environnement de contrôle s’aligne sur les lignes directrices du Centre pour les systèmes d’information de l’industrie financière (FISC). De nombreux contrôles décrits dans notre guide sont déjà mis en œuvre dans le cadre d’offres de conformité auditées par des tiers, telles que notre certification ISO/IEC 27001 et notre rapport SOC 2 de type 2.
Obtenir une copieSécurité de la plate-forme
Chiffrement des données clients
Protection des données des clients
Sécurité de l’API
Disponibilité du service
Tests de pénétration
Surveillance et réponse en matière de sécurité
Surveillance de la sécurité et réponse
L’activité administrative de Treasure Data au sein de l’infrastructure est saisie et surveillée par l’outil de surveillance des incidents de sécurité (SIEM) de Treasure Data. La couverture en continu est en place pour surveiller les alertes et l’activité SIEM.
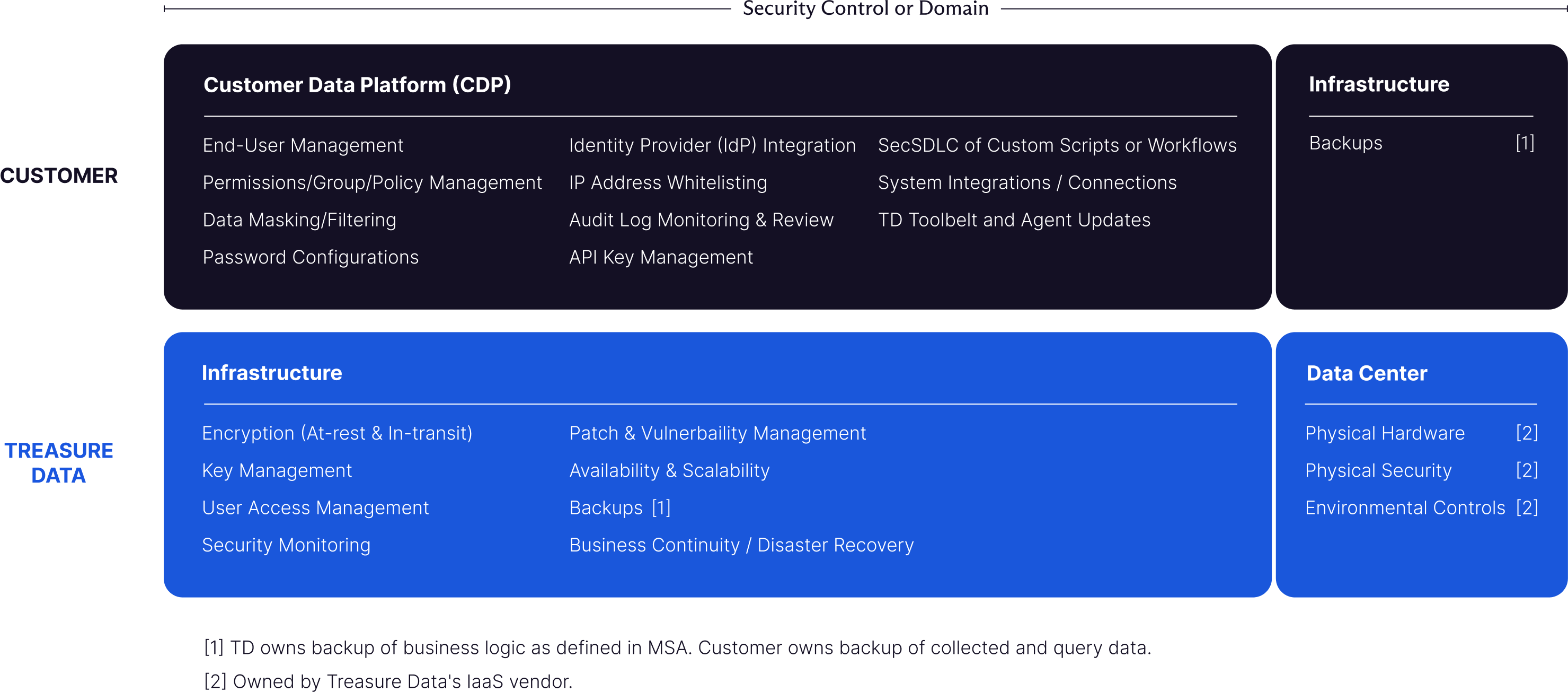
En savoir plusShared security model
Localisation des données
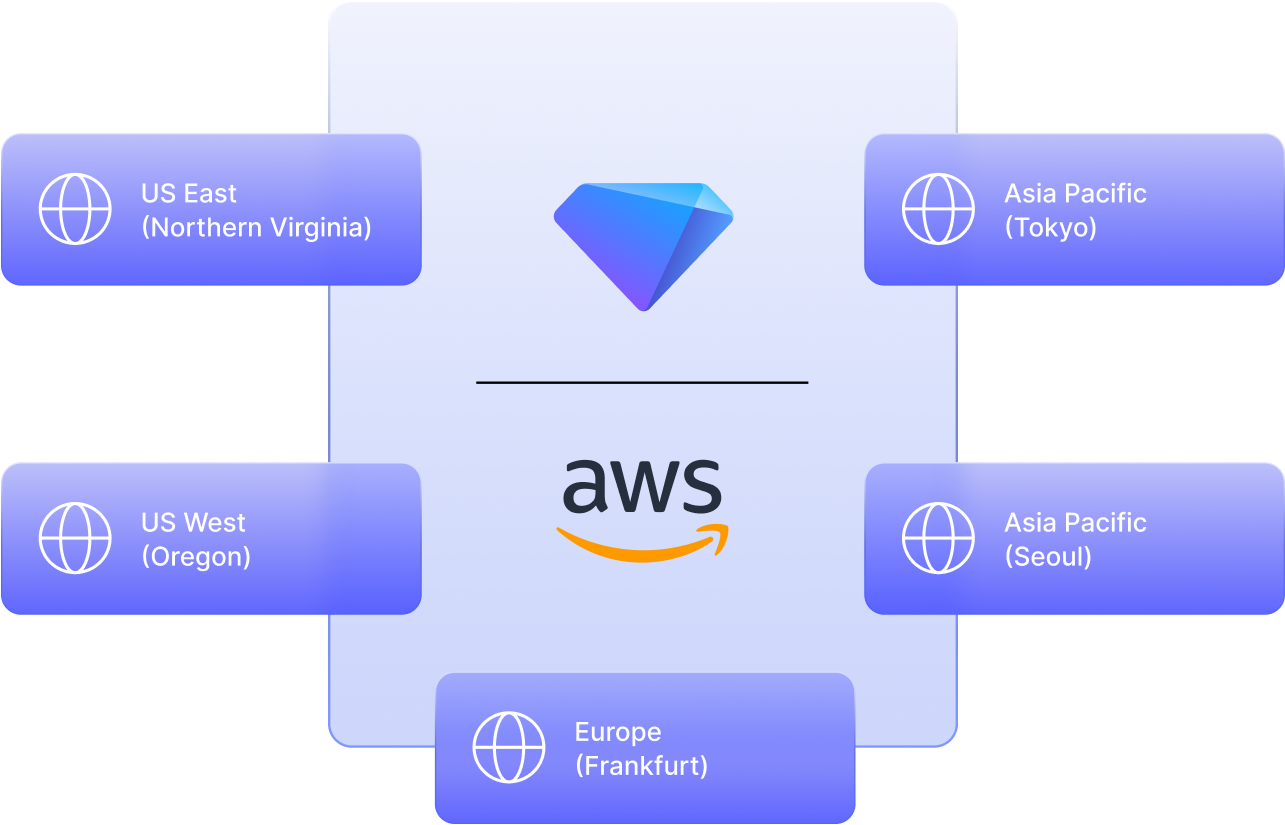
Tous les services d’infrastructure et de stockage sont exécutés dans les data centers régionaux d’AWS et s’appuient sur plusieurs zones de disponibilité. Treasure Data utilise les régions AWS suivantes :
-
Est des États-Unis (Virginie du Nord)
-
Ouest des États-Unis (Oregon)
-
Europe (Francfort)
-
Asie-Pacifique (Tokyo)
-
Asie-Pacifique (Séoul)
Au-delà de la conformité : Notre approche de la sécurité
Consumer data is gold and should be as safe and secure as any precious material.
Learn about how our comprehensive approach to security and privacy goes beyond compliance, helping global brands gain trust and see business value.








